Azure Front Door in 2026 and the Standard vs Premium Decision
In this article
When we wrote about Azure Front Door in 2019, the pitch was a global Layer 7 load balancer with built-in WAF and CDN. Seven years later, Microsoft has consolidated the product into two tiers: Standard and Premium. New classic Front Door profiles stopped being possible on 31 March 2025, classic managed certificates were cut off on 15 August 2025, and full classic retirement is scheduled for 31 March 2027. The architecture is the same global anycast service, but the feature set, pricing model, and integration points have changed enough to warrant a fresh look.
Standard vs Premium in Practical Terms
Both tiers provide global HTTP/HTTPS load balancing, SSL termination at the edge, URL-based routing, caching, compression, and the rules engine. Both tiers support custom domains with managed TLS certificates. Both tiers bill per request plus data transfer.
Where the tiers diverge is the part that matters for enterprise decisions.
Premium is the tier to choose when you need Private Link origins and the strongest security feature set, including bot protection and Microsoft Threat Intelligence-backed capabilities bundled with the WAF. Microsoft’s own comparison pages are not perfectly consistent on which exact WAF features sit on which tier, so the safe rule is: if your WAF strategy depends on bot management or threat-intel feeds beyond basic rate limiting, plan for Premium and confirm against current pricing and tier docs.
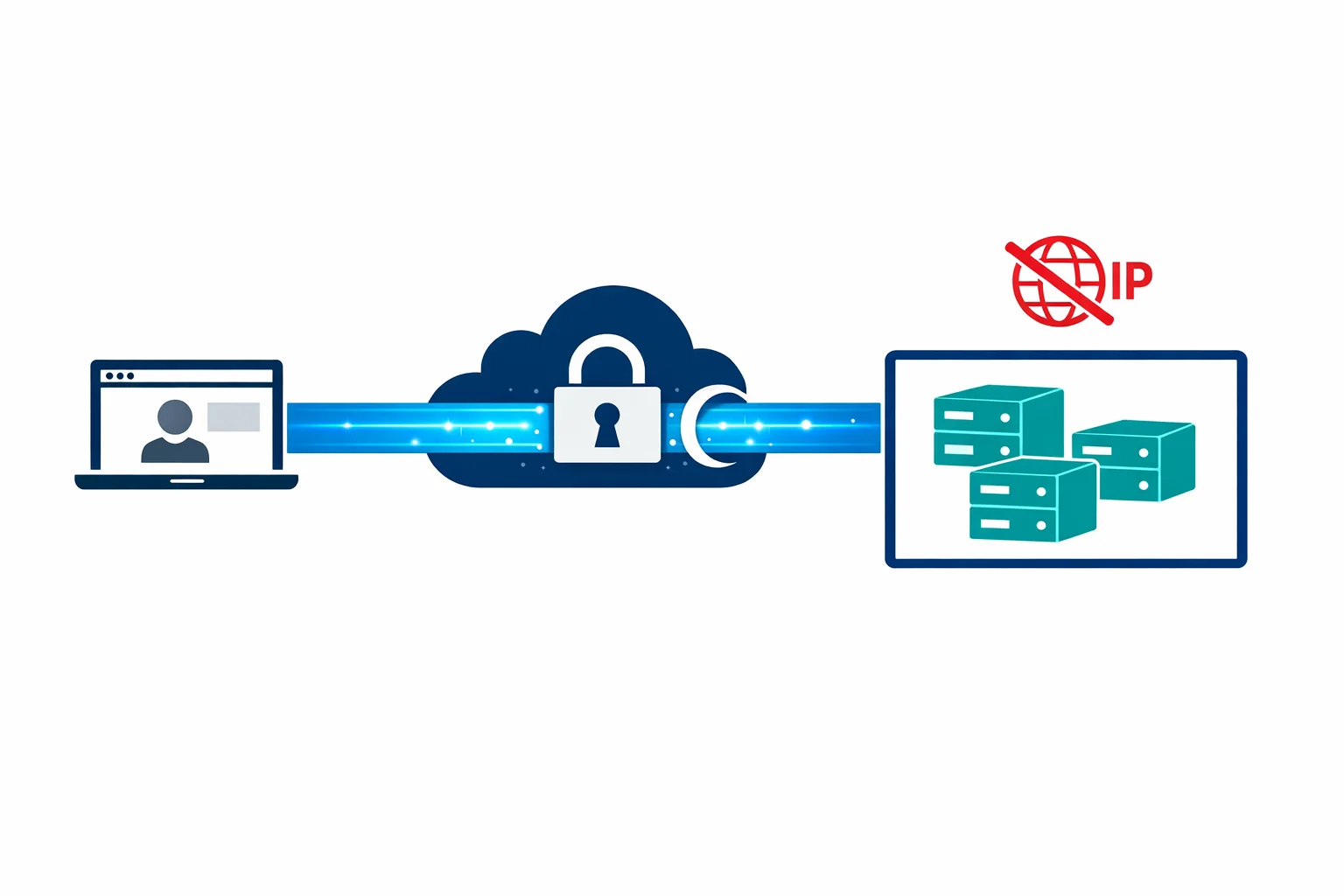
Private Link to origin is the feature that changed enterprise Front Door adoption. Premium supports Private Link origins, so Front Door reaches supported backends through a private endpoint instead of over the public internet. Standard does not.
Origin response timeouts are configurable up to 240 seconds on both Standard and Premium, with a 16-second floor. Timeout is not a Premium-only reason to upgrade.
Both tiers produce access logs and health probe logs. Premium adds WAF log enrichment with bot classification details, which feeds into WAF analysis workflows.
For most enterprise deployments, the decision comes down to one question: do you need Private Link to your origins? If yes, it is Premium. If you are serving a public-facing website or API where the backend has a public endpoint and you don’t need bot management, Standard covers the requirements at lower cost.
Private Link to Origin Changes the Architecture
Before Private Link origins, Front Door connected to backends over the public internet. Your App Service or Application Gateway needed a public endpoint even if the only legitimate traffic came from Front Door. You locked it down with access restrictions and header filtering, but the public endpoint existed.
With Premium, you can design the origin path so Front Door reaches supported origins privately, removing the need for a publicly reachable origin path in many cases. Microsoft documents Private Link support for App Service, Function App, Blob Storage and Static Website, internal load balancers (including AKS and Red Hat OpenShift), API Management, Application Gateway, and Container Apps. The common workaround of stacking Front Door in front of Application Gateway in front of the actual app (just to keep the backend private) becomes unnecessary unless you need Application Gateway’s specific regional capabilities.
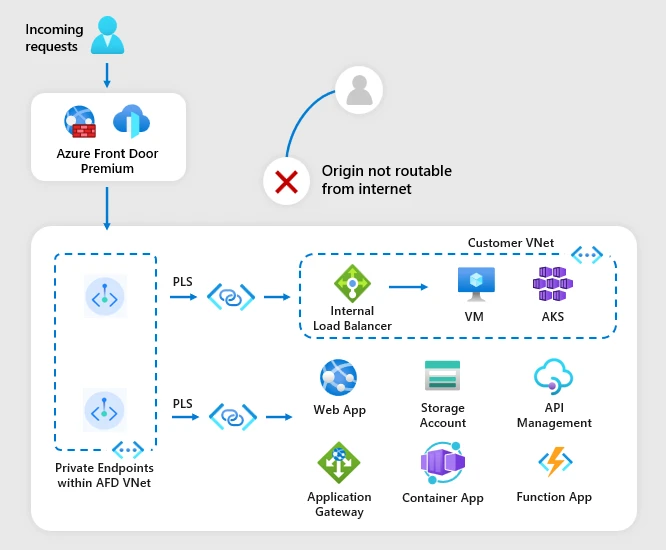
The setup requires approving the private endpoint connection on the backend side, either manually or through Terraform/Bicep.
Front Door Plus Application Gateway
In many deployments, one or the other is enough. Use both only when the edge and regional layers solve clearly different problems.
Front Door alone covers globally distributed apps that need edge caching, global WAF, and SSL termination. With Premium Private Link origins, the backend stays private without needing an Application Gateway in the path.
Application Gateway alone covers single-region apps that need a regional WAF, cookie-based session affinity, or URL rewrite. No need for Front Door’s global edge.
Stacking both makes sense when you need WAF at two levels. Front Door’s WAF catches volumetric attacks and bot traffic at the edge. Application Gateway’s WAF applies application-specific rules tuned to your backend. The other case is multi-region deployments where each region has its own Application Gateway with app-specific routing, and Front Door distributes traffic across regions through Private Link origins.
If neither case applies, pick one. Front Door for global reach, Application Gateway for regional control.
Front Door Plus APIM
For API workloads, Front Door and API Management form a two-tier edge pattern. Front Door handles global distribution, WAF, and DDoS absorption at the edge. APIM handles authentication, rate limiting, transformation, and backend routing. With Premium, Front Door can connect to APIM privately so APIM doesn’t need a public-facing virtual IP. Private connectivity to APIM is viable, but the exact design depends on APIM tier and the supported private-endpoint configurations (the gateway endpoint is supported, self-hosted and workspace gateways are not).
The cost consideration: you pay for both services. For high-volume APIs, model the combined cost. For lower-volume APIs where APIM’s built-in rate limiting is sufficient, adding Front Door may not be justified.
The Cost Model
Front Door billing has four meters that matter: a base fee per profile, incoming requests, outbound data transfer from edge to client, and outbound data transfer from edge to origin. Azure-origin-to-edge transfer is free.
Premium runs roughly 10x the base profile fee of Standard on current list pricing. Converted from US list at the 25 April 2026 USD-to-EUR rate, that is around EUR 32/month for Standard versus EUR 305/month for Premium per profile. EUR list pricing on the Azure pricing page varies by billing region and FX, so use these as order-of-magnitude figures and validate against your own subscription. Per-request charges are small individually but add up at scale: a few cents per 10,000 requests, varying by tier and region.
Data transfer is the component that can surprise you. Both edge-to-client and edge-to-origin are billable meters. For applications serving large files, video, or high-bandwidth API responses, transfer can exceed per-request charges by an order of magnitude. The edge-to-origin meter often gets ignored in early estimates and then shows up in the bill once cache hit rates drop.
Caching helps significantly. Requests served from Front Door’s edge cache don’t hit your origin, saving origin compute, edge-to-origin transfer, and origin-to-edge load. If your content is cacheable, tune your cache rules aggressively.
For static websites and marketing sites, Front Door is often more expensive than Azure CDN for the same job. The premium is justified when you need WAF, complex routing rules, or Private Link to origin. For pure CDN use cases, evaluate whether you actually need Front Door’s capabilities. For a deeper meter-by-meter walk-through, Microsoft publishes a tier pricing comparison.
Migration From Classic Front Door
New classic Front Door profiles stopped being possible on 31 March 2025, and full retirement is scheduled for 31 March 2027. If you are still running a classic profile, migration to Standard or Premium should be on the roadmap now rather than 2027.
The migration tool handles most configurations, but watch for these differences:
The Rule Set replaces the classic rules engine with different semantics. Complex rule chains may need manual adjustment after migration. Caching now offers granular cache key configuration (include/exclude specific query parameters, headers, cookies), so test thoroughly if your app depends on specific caching behaviour.
The naming changed from “backend pools” to “origin groups.” In Terraform, this is not a property rename but a full resource replacement: azurerm_frontdoor becomes azurerm_cdn_frontdoor_profile, azurerm_cdn_frontdoor_endpoint, azurerm_cdn_frontdoor_origin_group, etc. Plan for state migration.
Custom domains need re-validation. WAF policies need migration to the Standard/Premium format, where they associate with security policies bound to endpoints rather than directly to the Front Door resource.
When Front Door Is Not the Answer
Single-region internal applications accessed only by corporate users over ExpressRoute or VPN don’t benefit from global edge routing. Application Gateway or a simple internal load balancer is sufficient. Applications serving east-west traffic between Azure services don’t need an edge load balancer either.
Low-traffic applications where the base profile fee exceeds the value of the capabilities (a static site with 1,000 visitors per month doesn’t need Premium at roughly EUR 305/month) are better served by Azure CDN or Application Gateway.
Front Door earns its cost on globally distributed public-facing applications where edge WAF, Private Link origins, and global failover are genuine requirements. For everything else, simpler options exist.
For the broader networking decision framework, see our comparison article.
Looking for Azure architecture guidance?
We design and build Azure foundations that scale - landing zones, networking, identity, and governance tailored to your organisation.
More from the blog

Azure Firewall in 2026 and When Standard, Premium, or an NVA Is the Right Call
Azure Private Link: How It Changed the Enterprise PaaS Playbook