Palo Alto Cloud NGFW for Azure in 2026 and When It Beats Azure Firewall Premium
In this article
Two years ago, we ran a proof of concept with Cloud NGFW for Azure while it was still fresh out of GA. The verdict then was cautious: the product worked, but it had rough edges around IP addressing, public IP limitations, and VNet peering cost surprises. We recommended it selectively and kept VM-Series as the default for complex hubs.
That assessment has aged. Cloud NGFW in 2026 is a different product. Palo Alto has addressed most of the early limitations, expanded regional availability, and sharpened the Panorama integration. Meanwhile, Azure Firewall Premium has also improved. The question for enterprises is no longer “does Cloud NGFW work?” but “when does it beat Azure Firewall Premium, and when does it not?”
What Changed Since 2024
Multi-IP support. Cloud NGFW now supports multiple public IPs per resource, removing the single-IP constraint that blocked complex DNAT scenarios. For enterprises with multiple inbound services behind one firewall, this was the biggest blocker in the early days.
Subnet planning is still a design constraint. Cloud NGFW remains tied to delegated subnets, so existing hubs with tight address plans can still favour VM-Series or a greenfield hub design.
Logging improvements. Cloud NGFW logs can now be delivered to Azure destinations including Log Analytics, which makes Sentinel integration much cleaner than it was in the early releases. The workarounds for structured log forwarding that plagued early deployments are no longer necessary.
Performance transparency. Palo Alto now publishes clearer limits and quota data, including throughput guidance and SNAT scaling behavior, which makes capacity planning less opaque than it was in the early releases.
Terraform provider maturity. The azurerm_palo_alto_next_generation_firewall_virtual_network_panorama resource and related objects have stabilized. Infrastructure as Code deployments that were fragile in 2024 now work reliably, including rulestack creation, Panorama association, and DNS proxy configuration.
Cloud NGFW vs Azure Firewall Premium in 2026
Both are managed firewalls. Neither requires you to run VMs. The differences are in inspection depth, management model, and cost structure.
Application Visibility
Azure Firewall Premium classifies traffic at L3/L4 with FQDN-based application rules for HTTP/HTTPS. It knows you are talking to storage.blob.core.windows.net on port 443, but it cannot tell you whether the traffic is Azure Storage SDK calls or someone running a custom HTTPS tunnel over the same endpoint.
Cloud NGFW uses App-ID to classify applications beyond IP, port, and FQDN patterns. Where Azure Firewall Premium knows you are talking to a specific endpoint on port 443, App-ID identifies the actual application inside the traffic flow and lets you write policy against it. For environments where application-level segmentation matters (pharmaceutical GxP systems, financial trading platforms, healthcare workloads with data classification requirements), App-ID provides a level of application-aware control that FQDN rules cannot match.
Threat Prevention
Both products cover the mainstream managed-firewall threat prevention requirements. Azure Firewall Premium includes signature-based IDPS with Microsoft’s threat intelligence feed, TLS inspection, and URL filtering by category. Cloud NGFW includes Palo Alto’s Advanced Threat Prevention, WildFire sandbox analysis, and its own URL filtering and IDPS capabilities.
Cloud NGFW’s differentiation here is less about “basic protection vs advanced protection” and more about Palo Alto’s App-ID-driven policy model, its broader security-services ecosystem (WildFire, Advanced Threat Prevention, DNS Security), and Panorama-based operational consistency for teams already standardized on Palo Alto. Whether that ecosystem premium justifies the cost depends on your threat model and your existing security tooling.
Management Model
Azure Firewall Premium is managed entirely within Azure. Policies are Azure resources, logs go to Log Analytics, and everything fits the Azure RBAC model natively. If your security team lives in the Azure portal, this is the path of least resistance.
Cloud NGFW can be managed through Azure (rulestacks as ARM resources) or through Panorama. For organisations running Palo Alto on-premises, Panorama gives you a single policy management plane across physical appliances, VM-Series instances, and Cloud NGFW. One change process, one audit trail, one team.
If you don’t have Palo Alto anywhere else, adding Panorama for one Azure deployment is probably not worth it. The Azure-native rulestack management is sufficient.
Cost
Azure Firewall Premium pricing is straightforward: a deployment-hour charge plus a per-GB processed charge. The numbers vary by region and contract, but for most European deployments it lands in a predictable range that is easy to model.
Cloud NGFW pricing is tied to the Palo Alto service model and the surrounding Azure network path, so the comparison is not just “firewall list price vs firewall list price.” The Palo Alto service charge sits on top of Azure network-transfer costs that come from the delegated-subnet architecture. In many enterprise patterns, Cloud NGFW lands materially above Azure Firewall Premium once you include both components.
Validate both against your region, contract, and traffic profile before making a commitment. The cost gap is real, and it buys you App-ID, the Palo Alto security-services ecosystem, and Panorama integration. For organisations that don’t need those capabilities, Azure Firewall Premium is the simpler and cheaper answer.
Architecture Patterns That Work
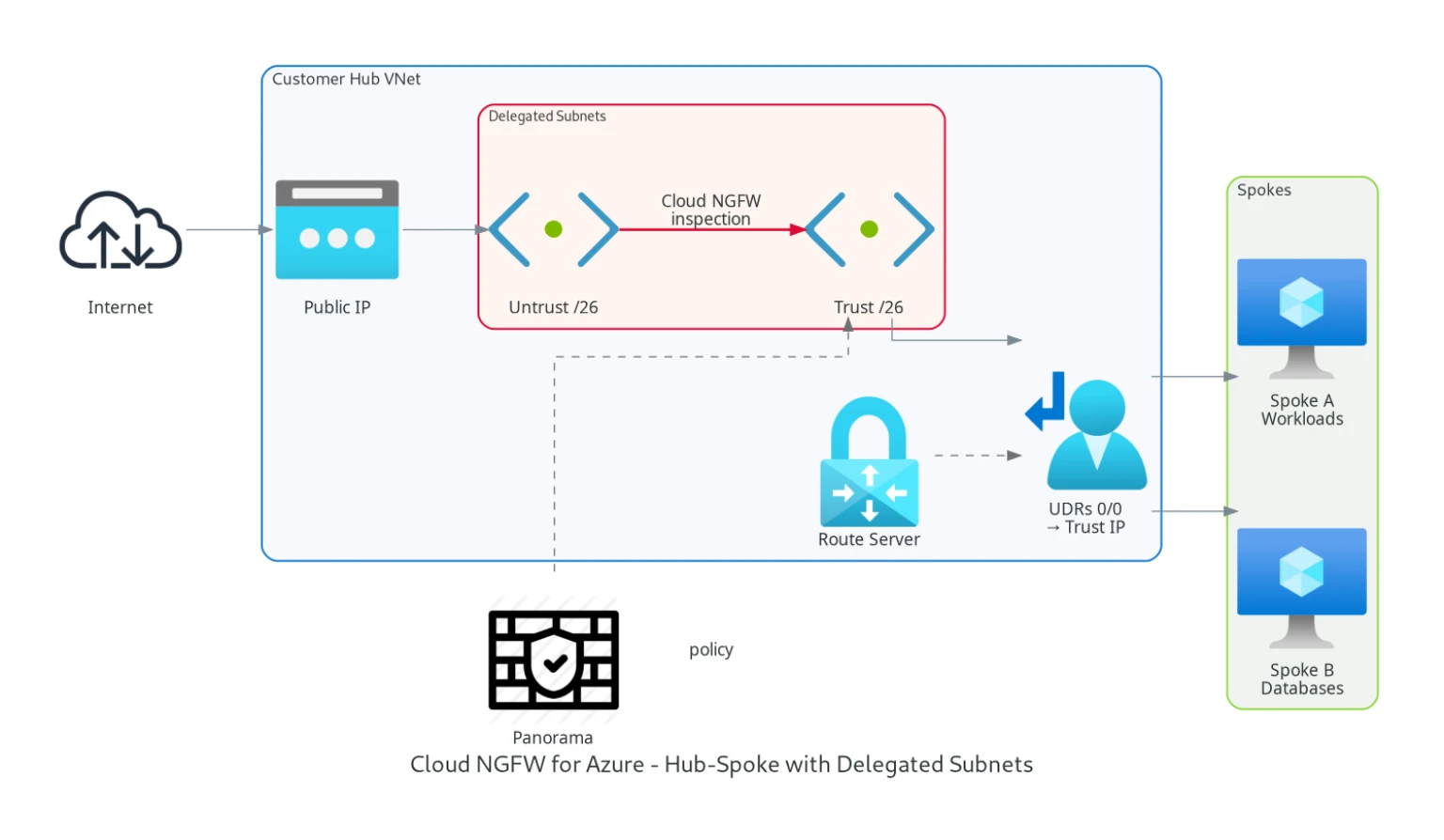
Hub-Spoke with Cloud NGFW
Cloud NGFW sits in the hub, receiving traffic via UDRs on spoke subnets. Spoke subnets have a default route (0.0.0.0/0) pointing to the Cloud NGFW trust interface. All outbound, inbound, and east-west traffic flows through the firewall.
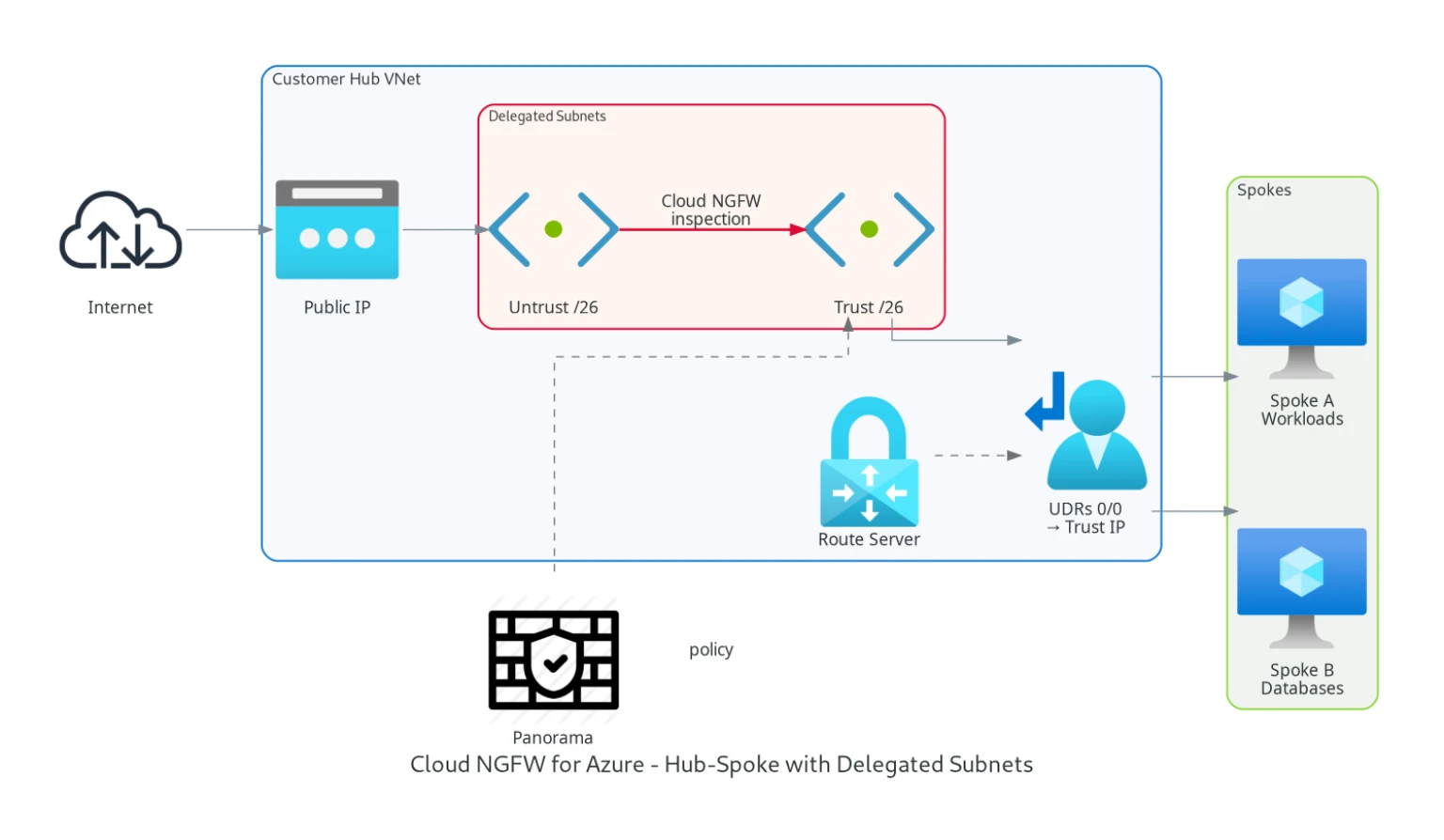
Identical to how you would deploy Azure Firewall or VM-Series. The UDR model doesn’t change. What changes is that you configure the rulestack instead of firewall policy, and App-ID rules replace FQDN application rules.
SD-WAN Integration
For environments with Cisco, Fortinet, or other SD-WAN routers in the hub, Cloud NGFW works the same way VM-Series did. SD-WAN routers advertise routes through Azure Route Server, and UDRs force traffic through Cloud NGFW before it reaches spokes. Return traffic from spokes passes through Cloud NGFW before reaching the SD-WAN routers.
One operational note: Azure Route Server’s BGP hold timer is fixed at 180 seconds and cannot be changed. Failover between SD-WAN appliances can take anywhere from 1 to 180 seconds depending on where in the hold timer cycle the failure occurs. We measured 24-72 seconds in practice. This is not a Cloud NGFW limitation but an Azure platform constraint that affects any NVA integration.
Multi-Region
Cloud NGFW is a regional resource. For multi-region deployments, you need a Cloud NGFW resource in each region. Panorama handles centralized policy across regions, with Cloud Device Groups separating region-specific rules from the shared security baseline.
Cross-region traffic (hub-to-hub) passes through the local Cloud NGFW on each side. VNet peering between hubs carries the traffic, and each firewall inspects its local direction. Azure global VNet peering and transfer costs apply in addition to the firewall service cost, so multi-region designs need careful cost modelling.
Decision Framework
Choose Azure Firewall Premium when your policies can be expressed in IP, port, and FQDN terms. When your security team works primarily in Azure. When you don’t have Palo Alto elsewhere. When cost optimization is a priority.
Choose Cloud NGFW when you need App-ID level application control that FQDN rules can’t express. When you already run Palo Alto on-premises and want Panorama for unified management. When your compliance framework names Palo Alto as an approved product. When your threat model justifies the additional investment in ML-based threat prevention.
Choose VM-Series when you need full control over the firewall infrastructure, specific PAN-OS versions for compliance, or when hub IP addressing constraints make subnet delegation impractical. VM-Series also remains the choice for extremely high-throughput environments where you need to benchmark and validate exact performance numbers.
For many new Azure deployments without an existing Palo Alto operating model, Azure Firewall Premium is the default starting point because it is simpler and usually cheaper. Cloud NGFW wins where App-ID-driven policy, Panorama standardization, or Palo Alto-specific security and compliance requirements materially change the outcome.
Related: Azure Firewall in 2026: Standard vs Premium, and When It Replaces an NVA the Azure-native side of this decision · What a Pharma PoC Revealed About Cloud NGFW the 2024 PoC that started this evaluation · Shared vs Separate Azure Hubs for NIS2 and DORA firewall separation in regulated environments
Need help with your Azure security posture?
We help enterprises design and tune Azure security controls: WAF policies, Sentinel ingestion, Defender for Cloud, identity governance, and NIS2/DORA readiness.
More from the blog
Palo Alto Cloud NGFW on Azure and What a PoC Revealed About the Managed Firewall

Azure Front Door in 2026 and the Standard vs Premium Decision